This blog is part of the VTPP (VNET Threat Perception Platform) project, a three-year programme co-funded by the European Commission under the DIGITAL-ECCC-2022-CYBER-03 call. The project covers DDoS mitigation with FastNetMon, vulnerability scanning with OpenVAS, custom AI/ML detection plugins for Zeek, HSM-backed key management, RPKI validation and a Krill CA, and a full-scale deployment of Security Onion as the IDS/SIEM/NSM backbone.
In the modern cybersecurity landscape, maintaining a static defense is no longer sufficient. For a significant period, our organization managed vulnerabilities reactively, relying on external triggers like CVE mailing lists, vendor advisories, and CSIRT alerts to identify emerging threats. While these sources provided general awareness, they lacked internal context. We lacked a structured, measurable view of our own exposure, making it difficult to answer critical questions regarding which specific systems were vulnerable or how to effectively prioritize remediation.
To address these gaps, we transitioned toward a Zero Trust security model, where infrastructure integrity is continuously verified through automated testing. This transformation has allowed us to shift from a model of general threat awareness to one of proactive, continuous visibility.
Why Continuous Scanning Became Necessary
The volume of vulnerability disclosures has reached a point where manual oversight is no longer feasible. During our implementation period alone, the global number of published CVEs grew by approximately 40,000 new entries. This rapid expansion of the attack surface means that the window of risk for unpatched systems extends significantly if detection relies solely on ad-hoc assessments.
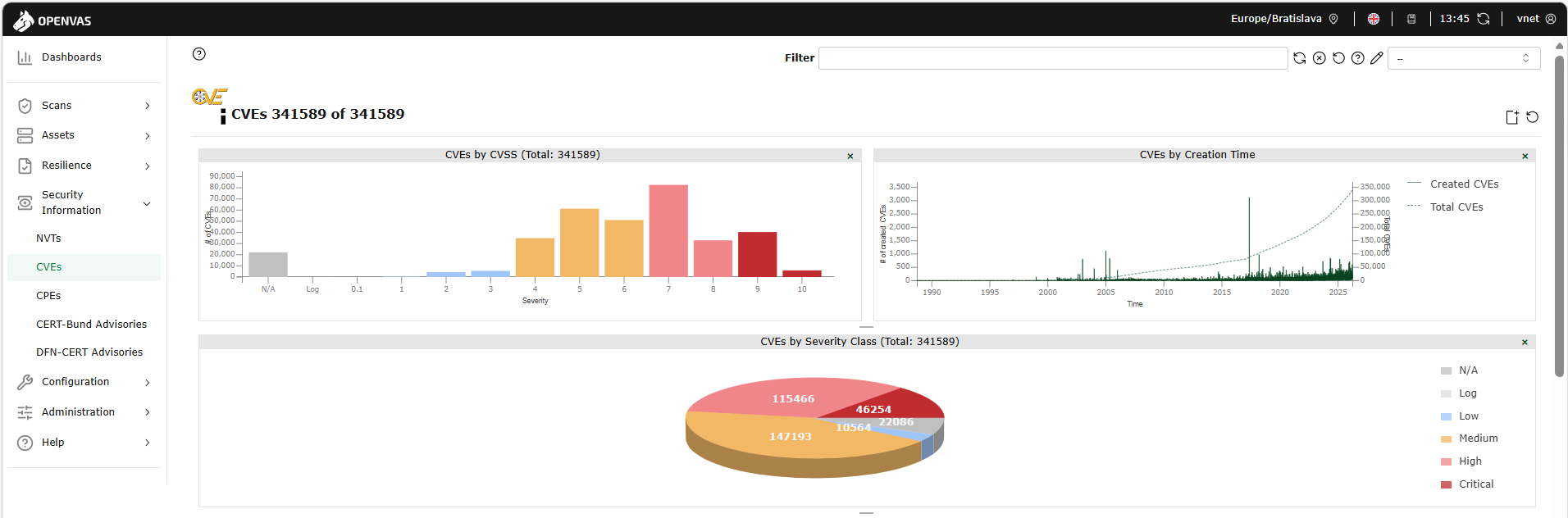
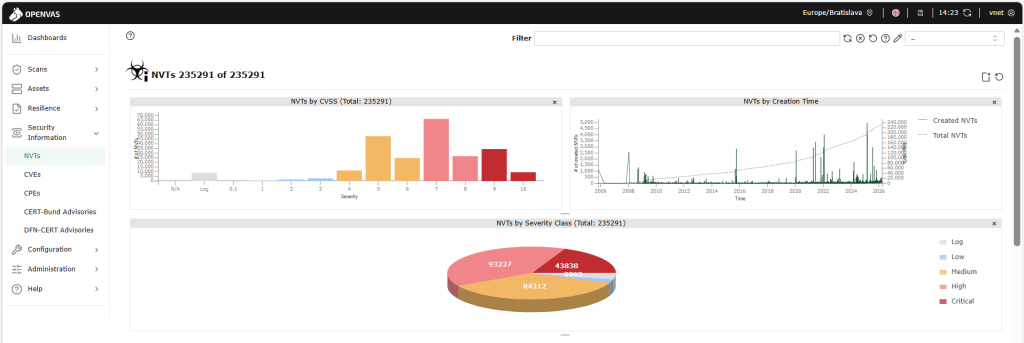
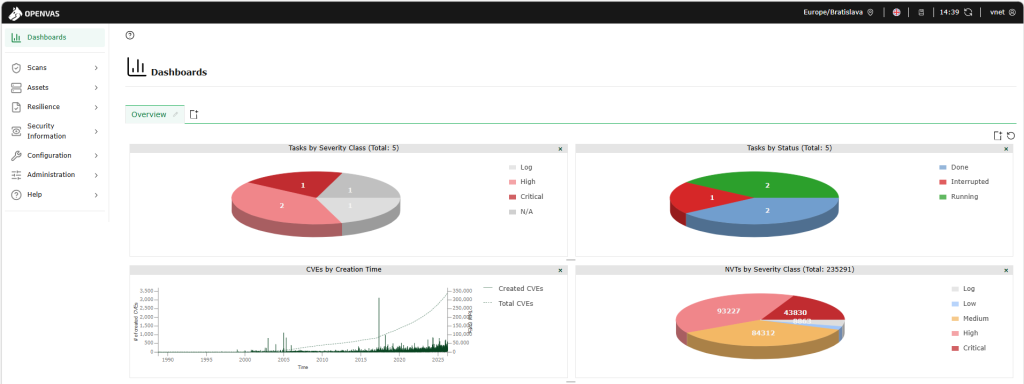
We required a systematic method to identify risks across our entire infrastructure. The objective was to establish a repeatable, data-driven security process that provides consistent output for analysis. After evaluating various solutions based on detection capabilities, update frequency, and scalability, we selected the Greenbone Enterprise (OpenVAS) platform. Our decision was driven by its robust detection engine and the Greenbone vulnerability feed, which provides over 200,000 Network Vulnerability Tests (NVTs) and CVE-based checks that are updated daily.
Building a Scalable Scanning Architecture
To ensure performance without disrupting production, we deployed the platform as a centralized virtual appliance within our internal environment. This placement provides the scanner with necessary routing access to all subnets while keeping management interfaces restricted to authorized personnel.
We tailored our scanning strategies to balance depth with operational stability:
Network Infrastructure: We utilize specialized CVE scans for routers, firewalls, and switches. These focus on identifying known vulnerabilities in detected services, ensuring visibility without placing excessive processing load on critical network hardware.
Servers: We apply the „Full and Fast“ profile, which includes service and version detection and misconfiguration checks. Crucially, we exclude intrusive brute-force testing to prevent service degradation or accidental account lockouts.
Closing the Coverage Gap: Asset Onboarding
A scanning solution is only effective if it covers the entire environment. To prevent „dark assets“ from remaining unscanned, we implemented a defined onboarding process. This process ensures that every new host added to our internal asset inventory is systematically integrated into the relevant scan scope from its initial deployment. By categorizing assets into specific groups (Network vs. Server) during onboarding, we ensure they immediately receive the appropriate level of scrutiny.
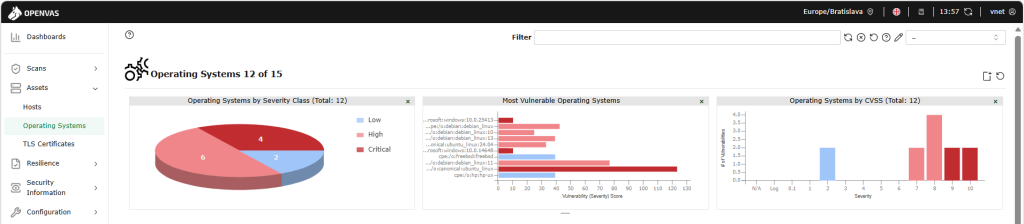
Measurable Outcomes: What the Scans Revealed
Transitioning to continuous visibility provided immediate, actionable data. Our initial automated scans identified several high and critical vulnerabilities that had not been captured by previous manual processes. These findings allowed us to initiate prioritized remediation efforts:
Protocol Hardening: We identified and removed unencrypted management protocols (Telnet and FTP) on network devices, replacing them with secure SSH and SFTP alternatives.
Attack Surface Reduction: Scans revealed unnecessary NX-API exposure on our core network devices, which we successfully mitigated to close a potential attack vector.
Infrastructure Lifecycle Management: We flagged and decommissioned vulnerable Brocade SAN switches that were no longer supportable.
OS Migration: We identified several servers running End-of-Life (EOL) operating systems, allowing us to prepare replacement plans and apply interim mitigations where immediate upgrades were not feasible.
Efficiency Through Intelligent Automation
To manage the volume of scan data and prevent alert fatigue, we developed an internal automation tool to process raw results. Instead of reviewing exhaustive reports, our engineers receive structured data that highlights recurring issues and prioritized remediation recommendations. This reduces manual effort and accelerates our response to the highest-risk findings.
Roadmap and Conclusion
Our security posture has measurably improved, showing a significant reduction in critical and high-risk vulnerabilities. However, vulnerability management is an evolving process. Our future efforts focus on:
Legacy Decommissioning: Completing the replacement of identified EOL systems.
Scan Optimization: Refining configurations to further reduce noise and increase detection precision.
Continuous Validation: Maintaining full asset coverage as our infrastructure expands.
Implementing OpenVAS has moved our organization toward a **continuous, measurable security control** model. We no longer wait for external alerts to define our risk; instead, we identify potential exposures shortly after their disclosure, significantly reducing our reaction time and ensuring our defenses remain as dynamic as the threat landscape.

Views and opinions expressed are however those of the author(s) only and do not necessarily reflect those of the European Union or the European Cybersecurity Competence Centre. Neither the European Union nor the granting authority can be held responsible for them.
